November 16th, 2023 by admin
In the digital age, email has become the lifeblood of business communication. The channel helps build relationships with clients and make final decisions, and vital information flows through it.
However, this essential tool is also a prime...
Read Full Story »
Tags: business, security threats, security
Posted in: Security
June 9th, 2020 by admin
With businesses moving to a remote workforce, they face different challenges that they didn't deal with before. One of those challenges is how to keep your network secure while operating under a remote model. Here are some recommendations to ensure...
Read Full Story »
Tags: anti-virus, business, cyber security, data protection, email, password, security threats, security, Solutions, technology
Posted in: Services, Security, Solutions
January 16th, 2020 by admin
Protecting your data networks is one of the most important things your company can do. At ATS, our
experience and expertise enable us to bring the most innovative cybersecurity solutions to the table.
There are numerous types of cyberattacks,...
Read Full Story »
Tags: data protection, security threats, security
Posted in: Services, Security
January 9th, 2020 by admin
Network security is a hot topic nowadays, and rightfully so. Protecting your data networks from hackers is one of the most important things your business needs to do. But, has your company taken the necessary steps to protect its physical location,...
Read Full Story »
Tags: security threats, security, Video Surveillance
Posted in: Security, Solutions
November 21st, 2019 by admin
As cyber-attacks continue to intensify, businesses are having a hard time finding skilled cybersecurity workers to protect their operations. The cybersecurity industry has taken a significant hit with the labor shortage causing many companies to fall...
Read Full Story »
Tags: anti-virus, cyber security, data protection, firewall, investment, IT Support , IT, malware, managed IT services, managed services, News, security threats, security, Solutions
Posted in: Managed IT Services, Support, Services, Security, Solutions
May 25th, 2019 by admin
Phishing attacks occur when communication that appears to be reputable is fraudulent. These sorts of scams are made to extract personal and sensitive information from victims such as social security numbers, addresses, bank information, and more. People...
Read Full Story »
Tags: cyber security, email, ransomware, security threats, security
Posted in: Security
May 9th, 2019 by admin
Throughout 2018 data breaches were a typical story from corporations of every size. The stories either tell of a breach that happened during the year or they're about ones that occurred years ago. Those common press releases about how their client's...
Read Full Story »
Tags: cyber security, data protection, security threats, security
Posted in: Services, Security
January 29th, 2019 by admin
Your business needs a dependable and robust cybersecurity solution, plain and simple. As technology continues to advance and new threats are coming to the forefront, it is essential to have the proper security and management behind you to ensure...
Read Full Story »
Tags: cyber security, safety, security reporting, security threats, security
Posted in: Security
December 21st, 2018 by admin
CONCORD, CA – ATS Communications a leading
managed technology services
provider (MTSP), is helping small
to mid-sized businesses (SMBs)
secure their organizations from
cyber-attacks, by addressing the
Windows 7 “End of Life” policy
that will begin...
Read Full Story »
Tags: cyber security, data protection, infrastructure, security threats
Posted in: Press Releases
November 20th, 2018 by admin
CONCORD, CA – ATS Communications a leading
managed technology services provider
(MTSP), is helping small to mid-sized
businesses (SMBs) protect themselves
and their customers from DNS
(Domain Name Server) attacks through
innovative technology...
Read Full Story »
Tags: data protection, network security, security threats
Posted in: Press Releases
November 15th, 2018 by admin
Security for your business is crucial. Everyone knows that, but settling for any old security system won't give you the protection you need against modern-day cybercriminals stealing sensitive data and monitoring operations. ATS offers great network...
Read Full Story »
Tags: network security, ransomware, security threats, security
Posted in: Security
June 26th, 2018 by admin
Making the switch to a Bring Your Own Device (BYOD) business environment extends well beyond the decision to let employees choose their devices. Your business should look at the pros and cons of the concept before deciding how to approach it and to what...
Read Full Story »
Tags: IT Support , IT, security threats, security
Posted in: Support
June 20th, 2018 by admin
Businesses have more to worry about than ever when it comes to dealing with new forms of cyber-attacks. The shift to a BYOD workplace adds even more challenges to protecting your digital assets. While hardware and software solutions continue to improve...
Read Full Story »
Tags: IT Support , IT, security threats, security
Posted in: Support, Security
May 14th, 2018 by admin
Technology improvements have made it easy for employees to get work done on their personal devices from anywhere. However, that freedom comes with additional security risks and requires extra diligence to keep data secure. Safeguarding information is...
Read Full Story »
Tags: cyber security, security threats, security
Posted in: Security
May 3rd, 2018 by admin
Often, businesses don't prepare for email disasters until after one has hit. But while email may comprise just a small part of a company's day-to-day operation, an email disaster can have a staggering impact on your business. The 2016 Democratic National...
Read Full Story »
Tags: data protection, data recovery, data security, email, security threats, security, services
Posted in: Security, Solutions
March 26th, 2018 by admin
While all employees need to be mindful of security, the nature of C-level executives makes them more attractive targets for hackers. That means it's necessary for them to take greater precautions.
According to TechRepublic, C-level executives are more...
Read Full Story »
Tags: business, cyber security, data protection, data security, security threats, security, Solutions
Posted in: Security
March 13th, 2018 by admin
The Mirai botnet refers to a massive-scale network of Linux-running Internet of Things devices turned into remote-controlled bots through a malware infection. Hackers can use the network to run a distributed denial of service, or DDoS, by having the infected...
Read Full Story »
Tags: cyber security, hacking, malware, security threats, security
Posted in: Security
February 12th, 2018 by admin
At the end of 2017, the world learned about Spectre and Meltdown: two far-reaching security threats that exploit how CPUs work to expose protected information on nearly every recent PC, server and smartphone. Hackers can use these exploits to do things...
Read Full Story »
Tags: data protection, data security, hacking, IT Support , IT, security threats, security
Posted in: Security
January 29th, 2018 by admin
Financial services companies should embrace a healthy dose of caution when implementing new fintech in their business. Fintech, or any technological innovation in the financial sector, is not inherently more or less secure than any other new technology,...
Read Full Story »
Tags: cyber security, hacking, IT Support , IT, security threats, security
Posted in: Security
January 16th, 2018 by admin
Hot off the tail of the massive 2017 Equifax breach that exposed personal information of 143 million customers, businesses are on high alert concerning IT security in 2018. While the IT security industry has been successful in mitigating and cracking...
Read Full Story »
Tags: anti-virus, hacking, IT Consulting, IT Security, IT Support , IT, security threats, security
Posted in: Security
October 24th, 2017 by admin
A new spear phishing technique, being used in a hacking campaign called FreeMilk, takes advantage of a Microsoft Office vulnerability in order to hijack existing email conversations to spread malware to high-profile targets. This new technique phishing...
Read Full Story »
Tags: desktop management, hacking, security threats, security
Posted in: Security
October 3rd, 2017 by admin
The 2017 Equifax hack is teaching a painful lesson about the necessity of businesses keeping up with software patches for IT security and to avoid catastrophic damage. The hack, which resulted in potentially exposing the financial information necessary...
Read Full Story »
Tags: IT Consulting, IT Security, IT Support , IT, security threats, security
Posted in: Security
July 25th, 2017 by admin
In June 2017, WikiLeaks released secret documents that exposed the tools the CIA uses to infiltrate public and private networks through routers. These documents have shined a light on how easy it is for someone to hack a router.
This begs the question,...
Read Full Story »
Tags: network security, network, security threats, security
Posted in: Managed IT Services, Security
July 11th, 2017 by admin
If your business is using 2-factor authentication or 2FA, methods to secure your important accounts, you may need to investigate better ways to implement the practice. Security experts widely recommend using 2FA, a system which utilizes a second security...
Read Full Story »
Tags: hacking, IT Consulting, IT Security, IT Support , IT, security threats, security
Posted in: Security, Knowledge
June 27th, 2017 by admin
Getting caught off-guard in a cyber security attack is a disaster for any business, large or small—and the frequency of attacks is only getting worse.
According to the CyberEdge 2017 Cyberthreat Defense Report, hackers successfully compromised...
Read Full Story »
Tags: cyber security, data protection, data security, security threats, security
Posted in: Support, Security
May 19th, 2017 by admin
As you may have already heard, there was a major ransomware attack across the globe recently. On May 12th, WannaCry/WCry 2.0 infected thousands of computers, taking the user's data hostage and demanding bitcoins to release it. We can't know how many...
Read Full Story »
Tags: cyber security, data protection, News, ransomware, security threats
Posted in: Support, Security
March 27th, 2017 by admin
We’ve been noticing an alarming trend regarding cyber security. Actually, more so a lack of security. One of the best practices on the frontline of security is your password. Unfortunately, this is an area that a lot of people will gloss over, often relying...
Read Full Story »
Tags: cyber security, password, security threats, security
Posted in: Services, Security
January 24th, 2017 by admin
Unlike most IT security threats, phishing scams attack the human element instead of the machine element. Phishing scams try to bait a person into exposing confidential information by posing as a legitimate, reputable source, typically by email or phone....
Read Full Story »
Tags: cyber security, IT Security, security threats, security
Posted in: Security, Solutions
December 21st, 2016 by admin
Phishing attacks are a dangerous and devastating method hackers use to steal personal information and accounts—primarily by striking the user instead of the machine. According to the APWG Phishing Activity Trends Report, the first quarter of 2016 saw...
Read Full Story »
Tags: cyber security, IT Consulting, IT Security, IT Support , IT, managed IT services, managed services, security reporting, security threats, security
Posted in: Managed IT Services, Security
December 7th, 2016 by admin
If your company’s antivirus software is letting you down, you should think twice before installing a second one on a computer: It may actually make things worse.
Multiple antivirus programs working in conjunction on the same device is not a case of...
Read Full Story »
Tags: anti-virus, backup, Backup Solutions, cyber security, disaster recovery, IT Consulting, IT Security, IT Support , IT, security threats, security
Posted in: Security
November 23rd, 2016 by admin
In September 2016, half a billion Yahoo account users received the bad news that their names, email addresses, phone numbers, and security questions were potentially stolen in a 2014 hack.
According to CNET, the Yahoo hack is the largest data breach...
Read Full Story »
Tags: cyber security, hacking, IT Consulting, IT Security, IT, password, security threats, security
Posted in: Security
November 1st, 2016 by admin
As you probably know already, the United States experienced its largest Internet blackout in history on October 21, 2016, when Dyn—a service that handles website domain name routing—got hit with a massive distributed denial of service (DDoS) attack...
Read Full Story »
Tags: IT Consulting, IT Security, IT Support , IT, network security, network, security threats, security
Posted in: Backup, Security
August 30th, 2016 by admin
Those old servers your business no longer uses—and keeps running anyway—are more than just a security risk: They’re hurting your firm’s bottom line.
The term comatose server describes a functional server, connected to a network, that sits idle virtually...
Read Full Story »
Tags: advice, security threats, security, servers
Posted in: Solutions, Knowledge
August 9th, 2016 by admin
There was a time when printers—in your office or home—were considered relatively "simple" office equipment: plug it in, connect it to the local network, and keep the ink fresh, and there wasn't much else to worry about.
But times have changed.
Today's...
Read Full Story »
Tags: network security, security threats, security
Posted in: Managed IT Services, Knowledge
July 12th, 2016 by admin
If you've looked over our previous posts since we've started our blog, you know how serious we are about protecting your company from everyday cyber-threats—mainly phishing, ransomware, and various other malware. Today we'd like to discuss a different...
Read Full Story »
Tags: cyber security, malware, network security, network, ransomware, security threats, security
Posted in: Managed IT Services, Solutions, Knowledge
July 7th, 2016 by admin
It's a fair bet that one of your employees has already shown off a trendy new wearable gadget around the office. What began with Bluetooth earpieces would branch off into smartwatches, smart glasses, wrist-worn fitness trackers, and even smart clothing...
Read Full Story »
Tags: devices, password, security threats, security
Posted in: Managed IT Services, Security, Knowledge
June 29th, 2016 by admin
Readers of our blog over the past few years know we were among the first in the Bay Area to warn our customers about the growing threats of ransomware—from the emergence of CryptoLocker and CryptoWall to our federal government's startling admission...
Read Full Story »
Tags: anti-virus, consulting, cyber security, data security, ransomware, security threats, security
Posted in: Support, Security, Knowledge
June 14th, 2016 by admin
A WISP is one of the most important documents for any company doing business over the Internet—which, in this day and age, is pretty much everybody. Who's responsible for drafting and maintaining your company's WISP? Or are you even sure what a WISP...
Read Full Story »
Tags: data protection, data security, security threats, security
Posted in: Security, Knowledge
June 1st, 2016 by admin
Being the cyber-security geeks we are, we took great interest in combing through this year's California Data Breach Report, released by the Attorney General's office this past February. The report tabulates data collected from breach incidents which...
Read Full Story »
Tags: cyber security, data protection, data security, malware, ransomware, security threats, security
Posted in: Data, Security
May 11th, 2016 by admin
Smartphone users can be broken down into two camps: those who can't live without lining up to buy the latest and greatest model the day it hits the stores, and those who hold on to their tried-and-true phone until it suddenly dies one morning.
There's...
Read Full Story »
Tags: advice, mobile, security threats, security, smartphones
Posted in: Security, Knowledge
May 3rd, 2016 by admin
Today we'd like to pass along a critical security advisory to all our customers:
If any of your company's Windows systems still retain Apple's QuickTime for Windows software, uninstall it immediately—as soon as you finish reading this post (if not...
Read Full Story »
Tags: advice, end of life, hacking, security threats, security
Posted in: Support, Security, Knowledge
April 26th, 2016 by admin
Earlier today the cashier at the local drive-thru miskeyed the amount of cash I gave him into his register. Somewhat sheepishly, he asked if I had a smartphone so I could verify the correct amount of change. Fortunately, I never leave home without it....
Read Full Story »
Tags: IT Consulting, IT Support , IT, mobility, security threats, security, smartphones
Posted in: Managed IT Services, Support, Knowledge
April 12th, 2016 by admin
A couple months back, we touched on the story of our normally tech-savvy friend who got tricked into allowing his desktop PC to be infected with obvious malware. At first, he had the sickening feeling that comes with a virus-infected computer—but thanks...
Read Full Story »
Tags: anti-virus, cyber security, malware, security threats, security
Posted in: Security
April 7th, 2016 by admin
We're only a few months into 2016, but we've already seen two high-profile ransomware attacks—where cyber-crooks heavily encrypt a victim's computer files before demanding payment for a decryption key only they can provide. Two notable incidents grabbed...
Read Full Story »
Tags: backup, Backup Solution, cyber security, ransomware, security threats, security
Posted in: Backup, Security, Knowledge
March 30th, 2016 by admin
If you think there's a new cyber-threat to worry about every week, you're probably right. The latest vulnerability to send shockwaves through the enterprise security community has been given a rather ominous acronym: DROWN, short for Decrypting RSA...
Read Full Story »
Tags: anti-virus, cyber security, hacking, security threats, security
Posted in: Security, Knowledge
March 23rd, 2016 by admin
Since Apple famously introduced the Macintosh over three decades ago, Mac users have been confident that their computers are virtually immune to ransomware and other malware threats which plague their Windows counterparts. But those days are over.
...
Read Full Story »
Tags: cyber security, hacking, malware, ransomware, security threats, security
Posted in: Security, Knowledge
March 15th, 2016 by admin
Hackers can take advantage of a newer technology prevalent throughout your business to break into your network and compromise security: Internet of Things devices. Your business may have never considered that the handy new Smart Thermostats throughout...
Read Full Story »
Tags: hacking, IT Consulting, IT Security, IT, security threats, security, smart devices
Posted in: Security
January 5th, 2016 by admin
What is the current state of your company's IT security training program—if you have one? Many companies settle for an annual group training session to broadly review the major types of cyber-threats—viruses, malware, and phishing.
The problem with...
Read Full Story »
Tags: cyber security, managed IT services, managed services, security threats, security, training
Posted in: Security
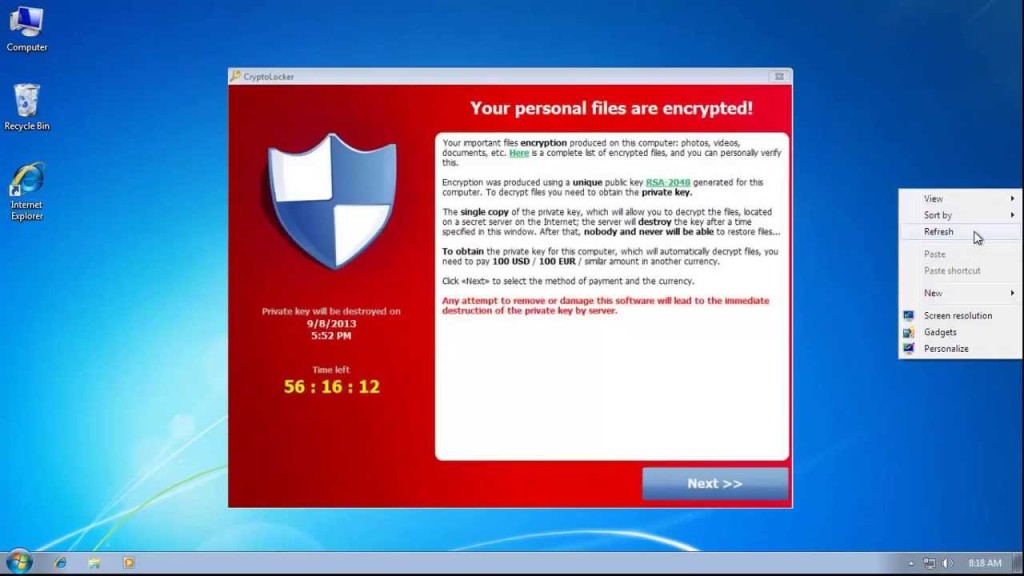
November 15th, 2013 by admin
CryptoLocker
CryptoLocker is a new, and particularly malicious, breed of ransomware discovered only a couple months ago. CryptoLocker is a Trojan horse malware that encrypts and restricts access to the infected computer while demanding payment for...
Read Full Story »
Tags: cyber security, ransomware, security threats, security
Posted in: Data, Security
July 22nd, 2013 by admin
Today's businesses are operating at a blistering pace and IT infrastructure has become the backbone of small to mid-sized businesses across the nation. The complexity and strain placed on networks has exposed SMBs to greater security threats than ever...
Read Full Story »
Tags: backup, disaster recovery, power outages, security threats
Posted in: Backup, Press Releases